Search results
There is a page named "Hacker" on this wiki. See also the other search results found.
Page title matches

File:Hacker-patent.jpg {{image-fairuse|a Kenner Centurions toy|Hacker (Centurions)}}(2,320 × 3,408 (1.1 MB)) - 23:13, 24 October 2017
File:Hacker-terror-strafer.jpg (400 × 304 (14 KB)) - 14:41, 17 June 2017
File:Hacker-terror-spare.jpg (400 × 304 (16 KB)) - 14:41, 17 June 2017
File:Hacker-box.jpg {{image-fairuse|a Kenner Centurions toy|Hacker (Centurions)}}(973 × 971 (358 KB)) - 15:47, 17 June 2017
File:Hacker-human.jpg {{image-fairuse|the ''The Centurions'' television series|Hacker (Centurions)}}(400 × 304 (9 KB)) - 15:09, 17 June 2017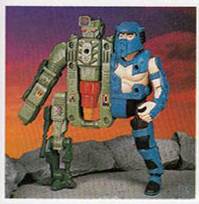
File:Traumatizer-hacker-toy.jpg {{image-fairuse|a Kenner Centurions toy|Hacker (Centurions)}}(199 × 204 (9 KB)) - 15:47, 17 June 2017-
496 bytes (88 words) - 20:00, 8 February 2021

File:Black Cyber Force Hacker - BCFH.jpeg (554 × 554 (28 KB)) - 04:37, 29 May 2021- 421 bytes (102 words) - 06:35, 25 October 2022
-
25 bytes (3 words) - 18:05, 17 December 2022
- ...ities in target systems, using the same knowledge and tools as a malicious hacker, but in a lawful and legitimate manner to assess the security posture of a2 KB (240 words) - 09:24, 17 August 2023
- {{Other uses|Hacker}} | name = Hacker9 KB (1,367 words) - 16:38, 30 August 2023

File:Portrait-anonymous-hacker-hacking-computer-system-cyber-crime-cyber-security-cybercrime 825385-825.jpg (826 × 551 (59 KB)) - 10:40, 9 September 2023File:BD HACKER GROUP.JPG (715 × 710 (14 KB)) - 08:39, 25 November 2023- | name = BD HACKER GROUP | image =BD HACKER GROUP.JPG2 KB (147 words) - 16:01, 25 November 2023
- #REDIRECT [[BD Hacker Group]]29 bytes (4 words) - 16:01, 25 November 2023
-
25 bytes (3 words) - 05:28, 1 January 2024
-
33 bytes (3 words) - 12:53, 17 February 2024
-
33 bytes (3 words) - 12:53, 17 February 2024
- | name = Fly Hacker {{verified}} | image = FLY HACKER.jpeg2 KB (273 words) - 05:31, 23 March 2024
Page text matches
- {{Other uses|Hacker}} | name = Hacker9 KB (1,367 words) - 16:38, 30 August 2023
- Here is a '''list of notable [[Hacker (term)|hacker]]s''' who are known for their hacking acts. ...ro|url=https://www.nytimes.com/1995/01/14/nyregion/reprogramming-convicted-hacker-his-line-friends-phiber-optik-virtual-hero.html|newspaper=[[The New York Ti15 KB (1,965 words) - 10:28, 3 March 2024
- ...ous modular weapons systems, and can exchange his Syntax cyborg system for Hacker's Lesion, or can combine with a Strafer or Traumatizer. He commands a massi Chief among his minions are his cyborg companion [[Hacker (Centurions)|Hacker]] and his daughter Amber. Other minions include the cyborg fish man [[Mako8 KB (1,161 words) - 12:16, 5 September 2019
- | name = Fly Hacker {{verified}} | image = FLY HACKER.jpeg2 KB (273 words) - 05:31, 23 March 2024

File:Jihadofficial9t9.jpg | occupation = {{hlist|Ethical Hacker|Web Designer|Freelancer}} '''Md. Jihad'' is an Ethical hacker , Digital Creator, Writer, digital marketer and also a writer for some time(783 × 1,280 (57 KB)) - 20:01, 20 July 2023- | title = [[Security hacker|Computer hacking]] | list2name = [[Hacker culture]] and [[Hacker ethic|ethic]]3 KB (325 words) - 06:58, 3 March 2024
- {{short description|Indian Ethical hacker}} | Niname = Indian Ethical hacker5 KB (639 words) - 08:40, 17 April 2023
- {{short description|Indian Ethical hacker}} | Niname = Indian Ethical hacker5 KB (639 words) - 07:36, 23 January 2024
- {{short description|Indian Ethical hacker}} | Niname = Indian Ethical hacker5 KB (662 words) - 15:40, 3 March 2024
- ...he Earth and turn its inhabitants into cyborg slaves. He is assisted by '''Hacker''', the cyborg sidekick and an army of cyborgs. There were many types of cy ...screen and cannons as well as a submarine drone were added. Doc Terror and Hacker are able to fly by swapping their purely robot half for a Strafer. They are19 KB (2,632 words) - 12:27, 28 June 2017
- | name = BD HACKER GROUP | image =BD HACKER GROUP.JPG2 KB (147 words) - 16:01, 25 November 2023
- ...ell]], but may have been used earlier in the hacker magazine ''[[2600: The Hacker Quarterly|2600]]''.<ref name="ollmann">{{cite web | author=Ollmann, Gunter ...ten using [[Cross-site scripting|cross site scripting]]. [[Security hacker|Hacker]]s may insert exploit kits such as [[MPack (software)|MPack]] into compromi119 KB (15,284 words) - 13:35, 3 February 2023
- ...yknight and Fireforce. With the Centurions gaining the upper hand, Terror, Hacker and Amber escape in a secret tunnel and set the mountain to explode behind | [[Hacker (Centurions)|Hacker]]5 KB (734 words) - 08:11, 14 July 2017
- | caption = Picture from debut film Hacker 2.0 | notable_works = Hacker 2.0 (2022)4 KB (472 words) - 18:48, 19 February 2023
- {{short description|Bangladeshi Cyber security researcher and Hacker, certified Network security fundamentals}} ...Security Fundamentals[[activist]]|[[Cyber Security Researcher]]|[[Security hacker]]}}7 KB (1,069 words) - 09:44, 14 June 2023
- * [[BANGLADESHI HACKER]] *[[BANGLADESHI HACKER]]4 KB (527 words) - 19:43, 10 September 2023
- * Ethical Hacker * Khan White Hat Hacker's Team2 KB (192 words) - 08:48, 29 March 2024
- ...the silver for Doc Terror's experiments. A vacationing Jake is captured by Hacker, and Amber tries to persuade him to join them. Jake escapes confinement, an *[[Ed Gilbert]] - [[Hacker (Centurions)|Hacker]]3 KB (514 words) - 09:57, 27 June 2017
- ...Bangladesh], [https://techtunes.co Techtunes BD]. He is certified ethical hacker and network security researcher. His most contents are based on technology. ...adays, he work alone without any team/group. He is one of the youngest top hacker of Bangladesh yet.8 KB (1,261 words) - 00:51, 8 February 2021
- ...Bangladesh], [https://techtunes.co Techtunes BD]. He is certified ethical hacker and network security researcher. His most contents are based on technology. ...adays, he work alone without any team/group. He is one of the youngest top hacker of Bangladesh yet.7 KB (1,118 words) - 06:14, 5 May 2021
